Pozq ransomware
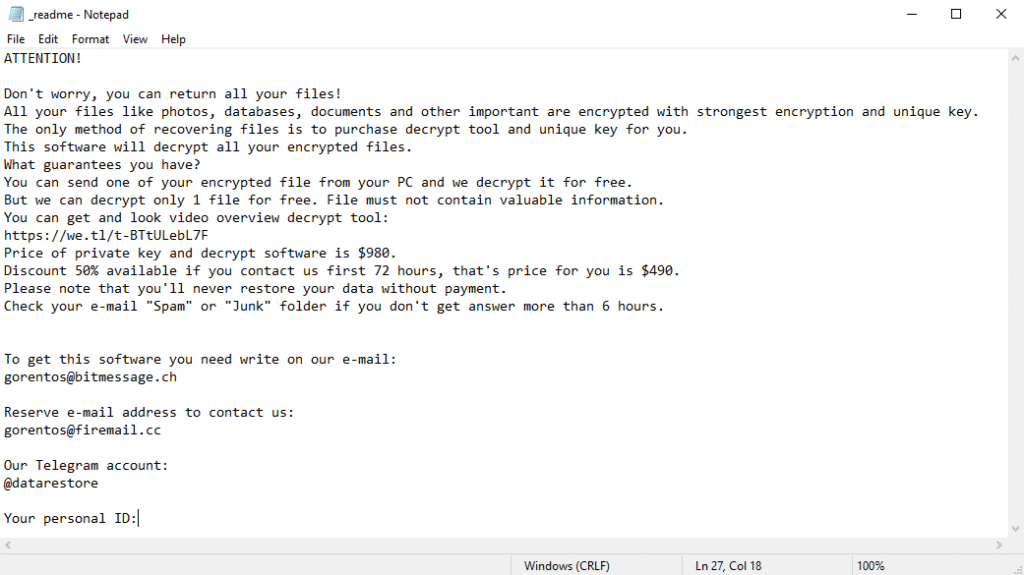
Pozq ransomware was recently discovered after a sample submission on VirusTotal. After some analysis, evidence was highlighted that Pozq may have a relationship with the Djvu group.
Pozq ransomware was recently discovered after a sample submission on VirusTotal. After some analysis, evidence was highlighted that Pozq may have a relationship with the Djvu group.
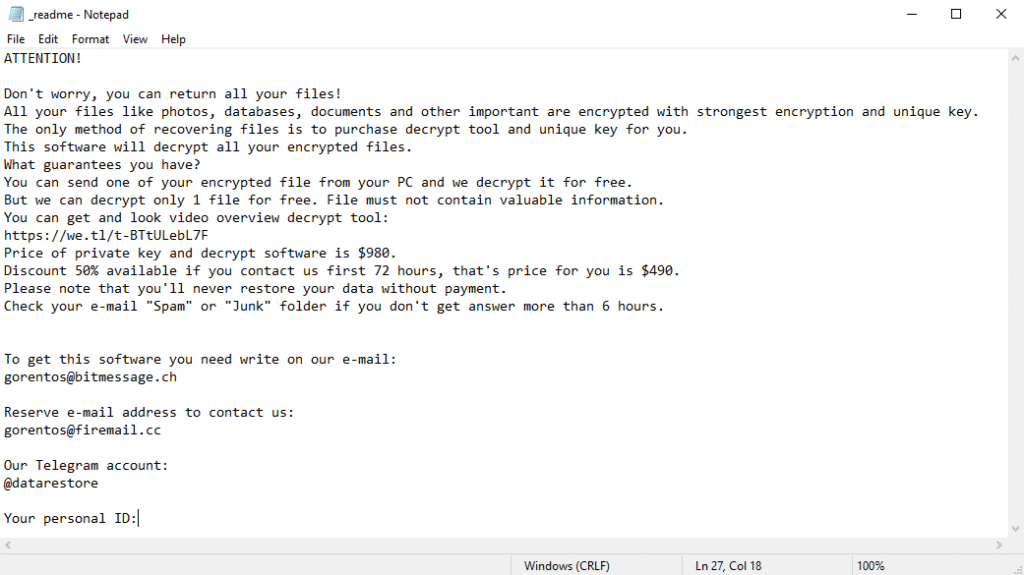
Buybackdate ransomware is the name of the newest extension that was discovered by cybersecurity researchers through VirusTotal. According to the experts, buybackdate belongs to the same ransomware family as ZEPPELIN.

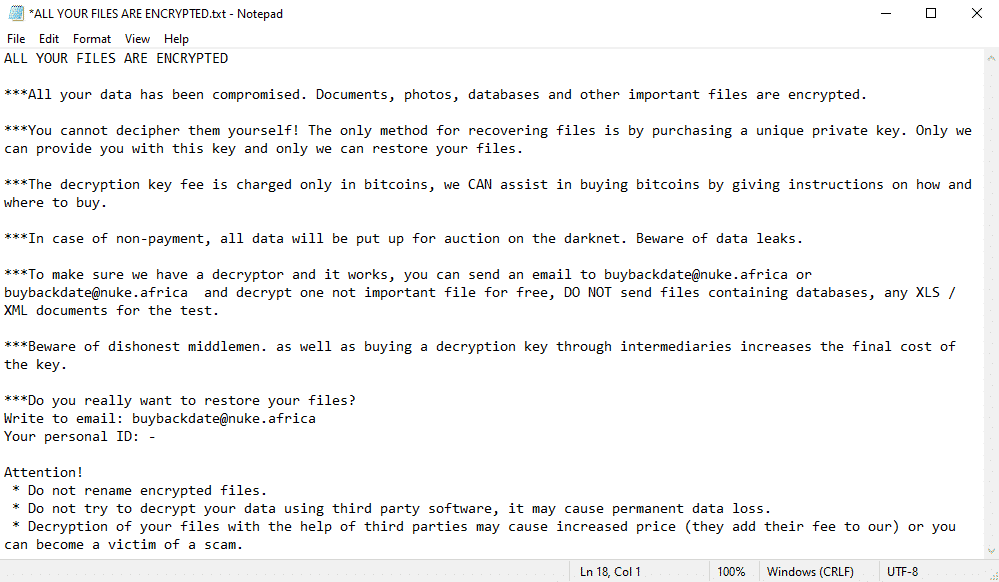
The RedKrypt ransomware has been active in recent days carrying out ransomware attacks. Researchers detected it by analyzing samples submitted to VirusTotal, an attack reporting platform.
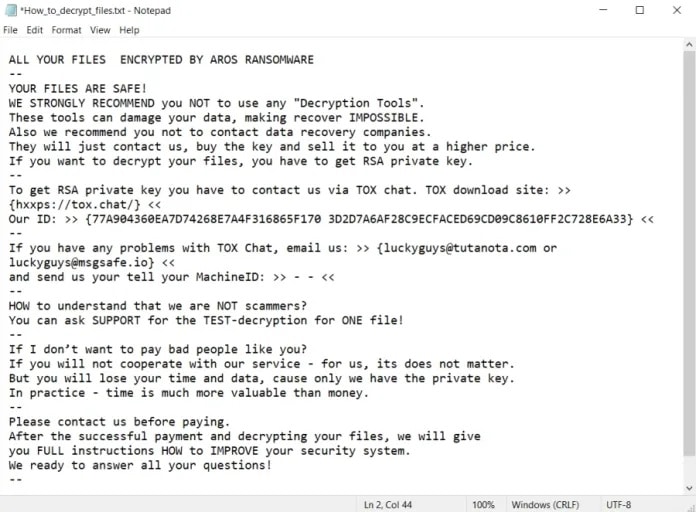
Ransomware AROS is the name of malware that has been carrying out attacks by encrypting victims and charging ransom to deliver their files back.
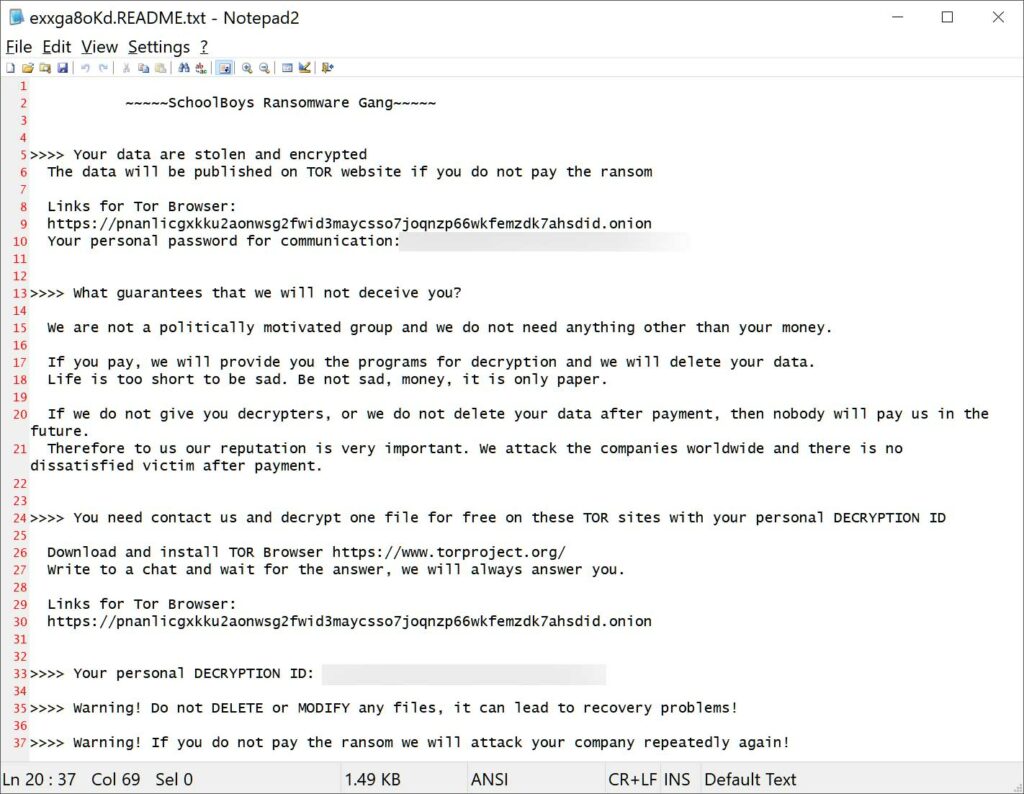
The SchoolBoys ransomware was identified in recent weeks by cybersecurity researchers and has already been drawing attention for the recent discovery of it being linked to the same hacker group as the TommyLeaks ransomware.
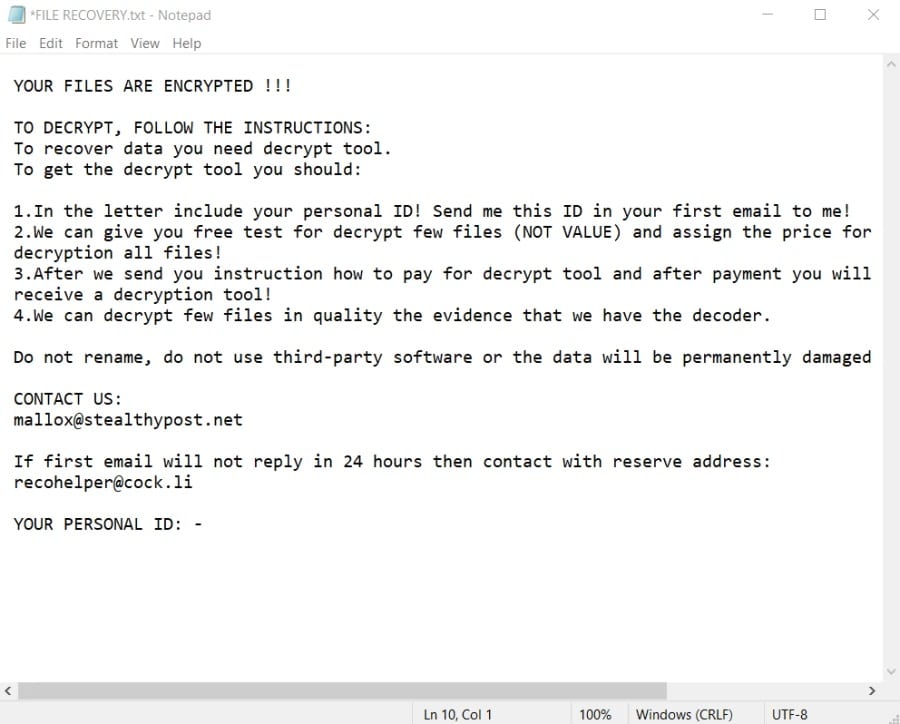
Fargo ransomware is malware that encrypts a victim’s data, leaving it absolutely inaccessible.
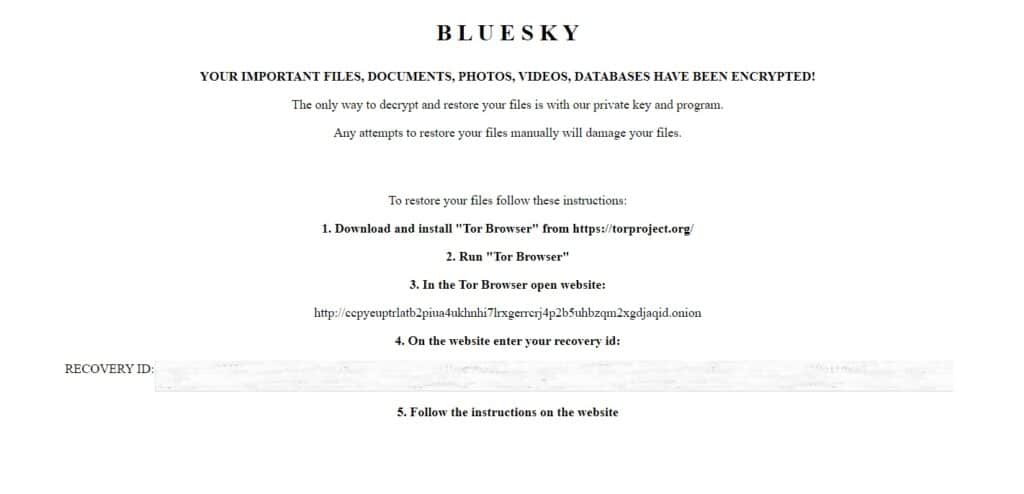
BlueSky Ransomware is a new extension discovered by researchers and has many similarities to another famous group, known as Conti.
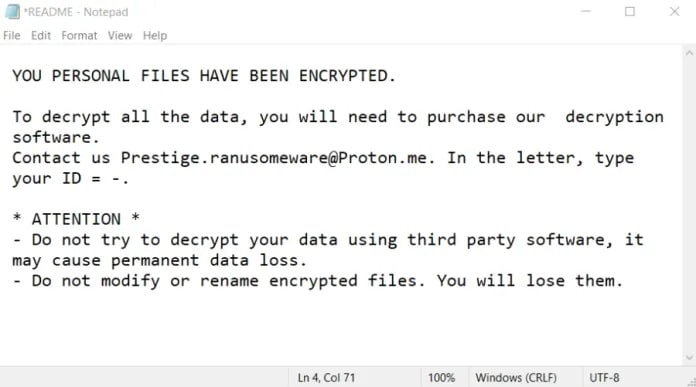
Prestige Ransomware is malware that encrypts files from an environment and makes them inaccessible to the user.
It has been active for the past few months and has harmed many businesses with its ransomware attacks.
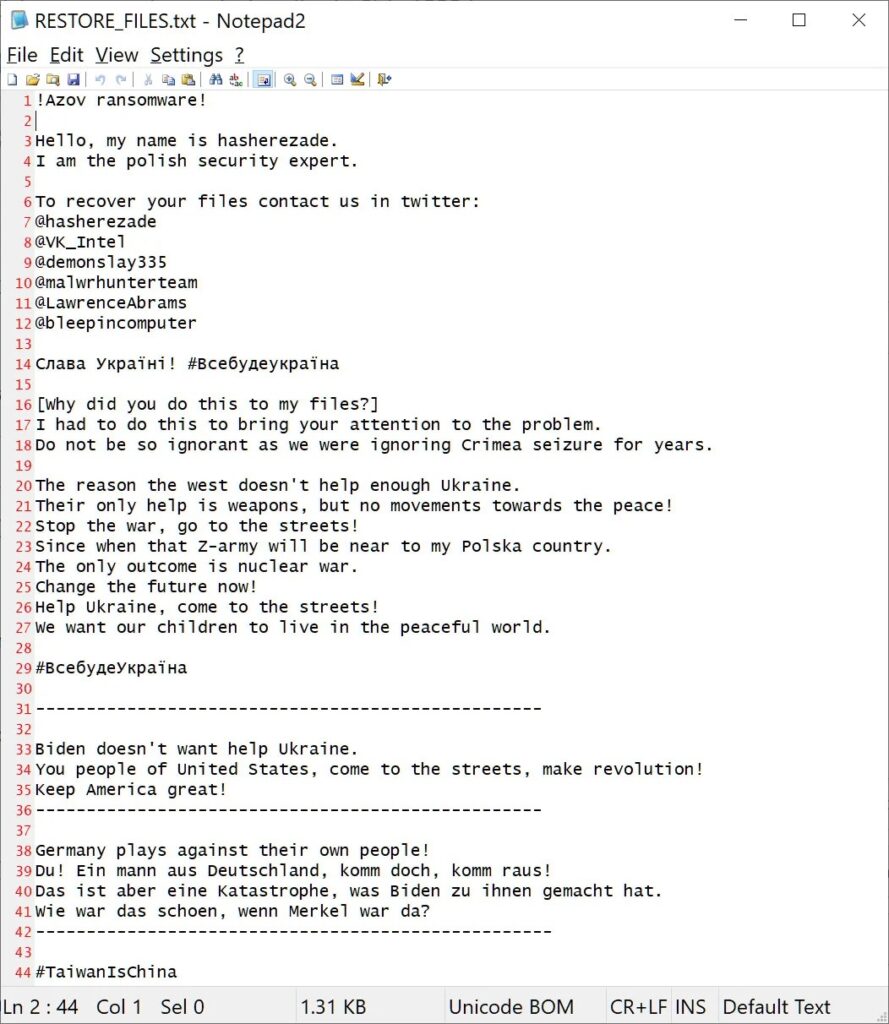
Azov Ransomware is a new destructive wiper extension that appeared in the month of October 2022. A peculiarity of this ransomware is that it is not an extortion operation as it does not charge ransoms, in fact, it only encrypts the victims’ data.
Storage is a set of hardware and software that helps you store, process and manage your data. Data storage can be used for both business and personal purposes.
Let`s Talk?
Through unique technologies Digital Recovery can bring back encrypted data on any storage device, offering remote solutions anywhere in the world.
Discover the invisible vulnerabilities in your IT – with the 4D Pentest from Digital Recovery
This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
These cookies are set to provide the service, application or resource requested. Without these cookies, your request cannot be properly delivered. They are usually set to manage actions made by you, such as requesting website visual elements, pages resources or due user login/logoff. We can also use these cookies to set up essential functionalities to guarantee the security and efficiency of the service requested, like authentication and load balancer request.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.
Performance Cookies
Google Analytics is a web analytics service offered by Google that tracks and reports website traffic, currently as a platform inside the Google Marketing Platform brand.
Please enable Strictly Necessary Cookies first so that we can save your preferences!