Expert Insights

Rever Ransomware
Ransomware attacks have been on the rise these past few years, and new ransomware often emerges. This July, it was the case with Rever ransomware that has some important characteristics. The main target of Rever ransomware is Synology NAS and Windows Server systems. After breaking in, most often done via unprotected RDP or malicious emails, the attackers encrypt the files
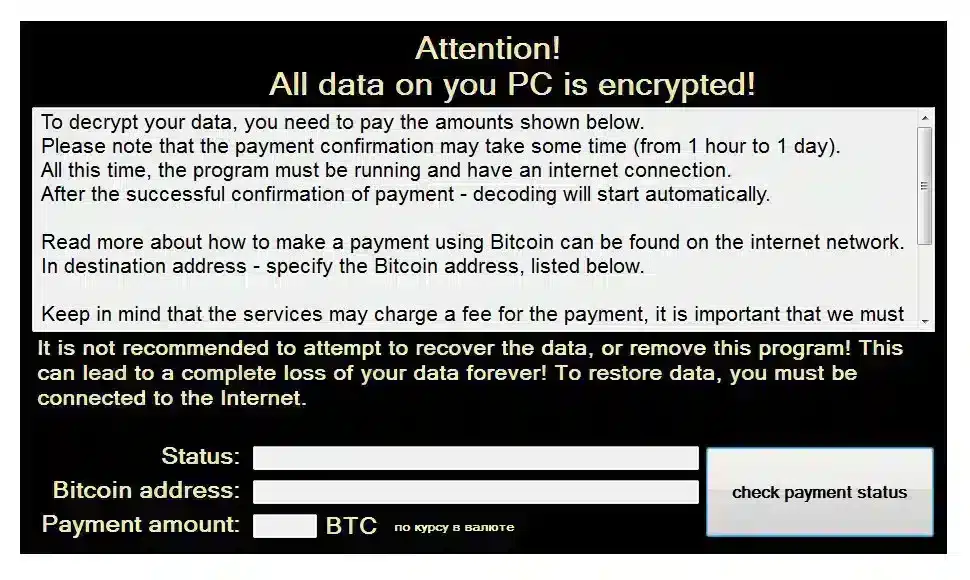
CryptOn Ransomware
The CryptOn ransomware was discovered around 2017. Since then, it has had varying nomenclatures, such as Cry9, CRY36, Cry128, Nemesis or X3M. CryptOn is part of the CryptoLocker ransomware family. CryptOn steals and encrypts the victim’s data. This way the group applies double extortion, which consists of threatening the victim with the publication of the data if the ransom is

OnePercent Ransomware
We know that the OnePercent ransomware has been active in the cyber world since late 2020. Based on Ransomware as a Service (RaaS) operations, the group behind OnePercent ransomware has been directing attacks on a number of companies around the world and largely in the United States. Like many other ransomware, OnePercent typically encrypts a company’s data, threatening to release

Boss Ransomware
Boss is a new ransomware extension discovered recently, but the group tends to grow rapidly due to its RaaS (Ransomware as a Service) strategy. The RaaS tactic has become a widely used method by hackers because it allows them to market the ransomware to anyone. Resulting in the highest profit and propagation of criminal operations. Boss brings a peculiar feature
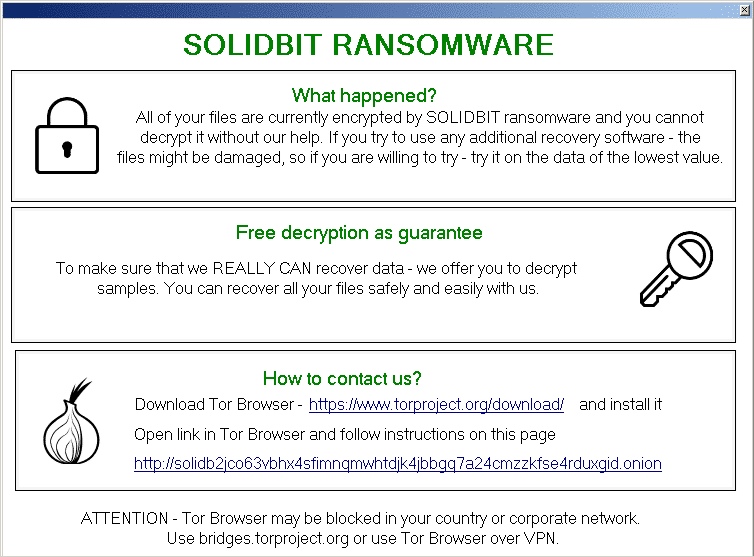
SolidBit Ransomware
SolidBit ransomware has recently emerged, targeting extort large and small businesses, the group behind SolidBit ransomware has been triggering attacks via email campaigns with malicious links and attachments. From the moment the environment is accessed, the attackers begin to encrypt files considered important and make them inaccessible to the user. Malware can also be transferred from one computer to another

Luna Ransomware
The Luna ransomware was discovered in June 2022, it is developed in the Rust programming language, preventing the group from being easily detected because the malware’s code does not remain static. This variation is capable of operating on multi-platforms, which allows the ransomware to attack on more than one operating system at the same time, including Windows, Linux and ESXi.
