Expert Insights
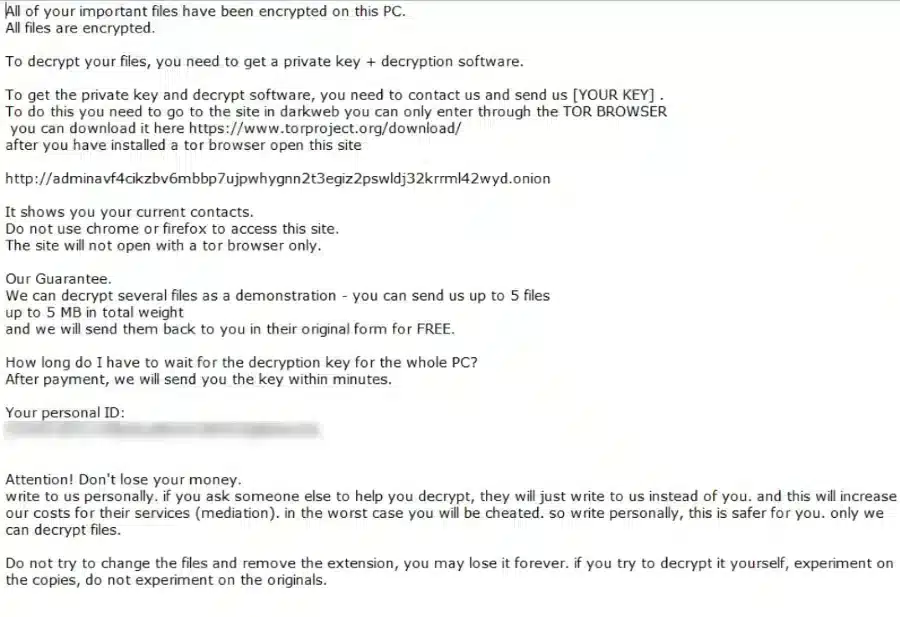
Admin Locker Ransomware
The Admin Locker ransomware was first seen in December 2021, the group uses a junction of the RSA and AES algorithms for encryption, this algorithm is extremely complex and produces a decryption key that only the group has access to. The Admin Locker targets all files stored on the device as well as backup system so that all possibilities to
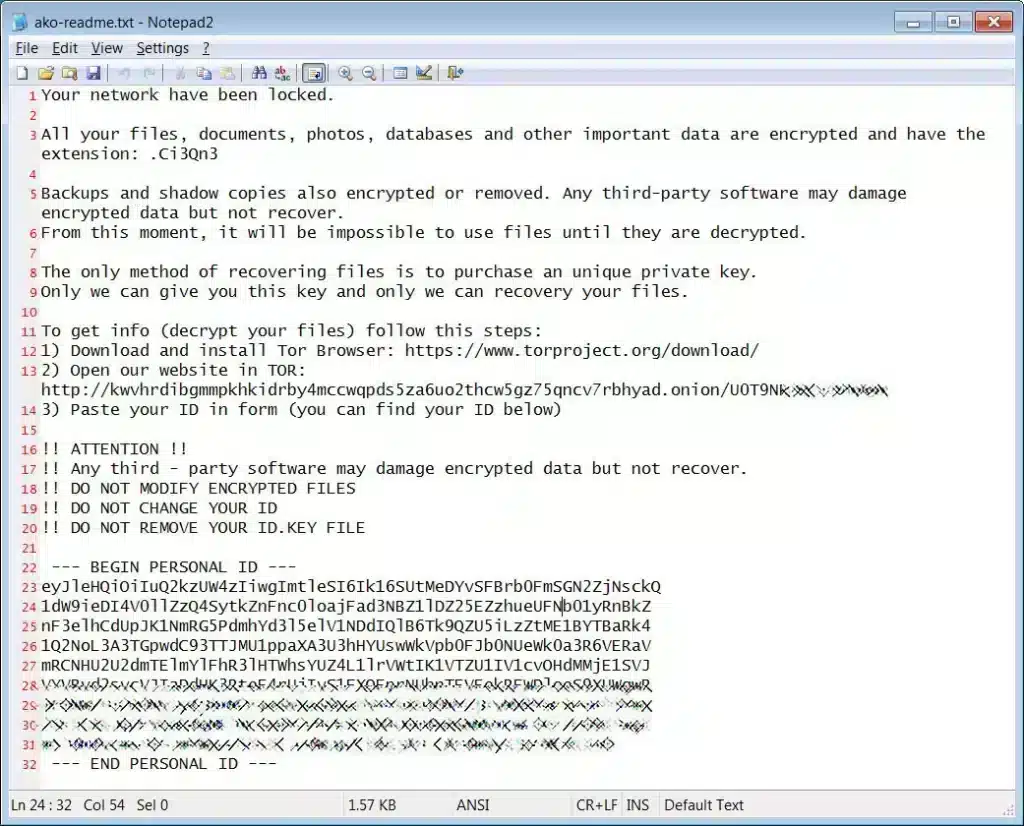
AKO Ransomware
AKO ransomware emerged in 2020, and since then a few variations have emerged, today there is an active variation responsible for numerous attacks around the world. Despite the changes and time the AKO group remains with the same tactics, double extortion remains in use. The group specialises not only in encrypting the victim’s data, but also in stealing it. After
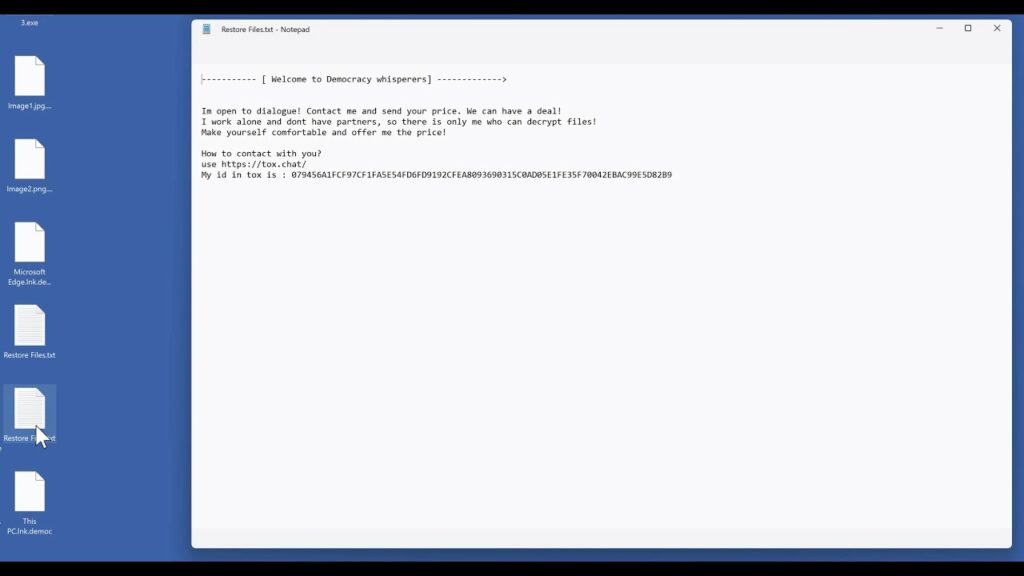
Democracy Whisperers Ransomware
The Democracy Whisperers ransomware, also known as Democ ransomware, has carried out numerous attacks around the world. The group has the ability to attack Windows and Mac operating systems. Democ uses varied tactics to break into the victim’s system like free software, spam emails, malicious links among others. The group is extremely damaging to the affected system, soon after the
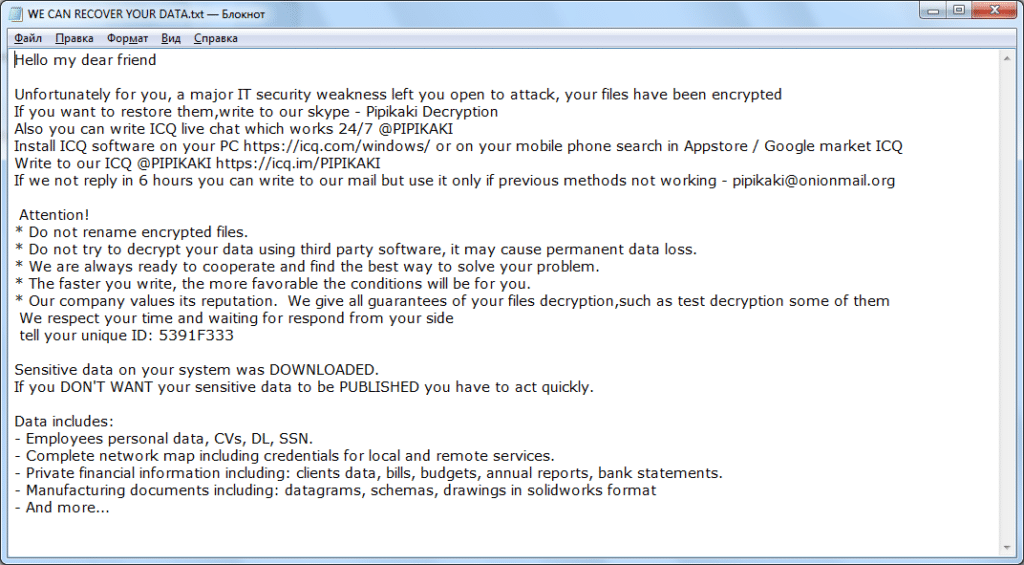
Pipikaki Ransomware
The Pipikaki ransomware has rocked forums across the internet with reports from numerous victims looking for solutions to the group’s encryption. Pipikaki has developed a powerful encryption algorithm, and not only that, the group uses tactics to break into a victim’s system ranging from brute force attacks to spam email campaigns. After invading the victim’s system, the ransomware disables the
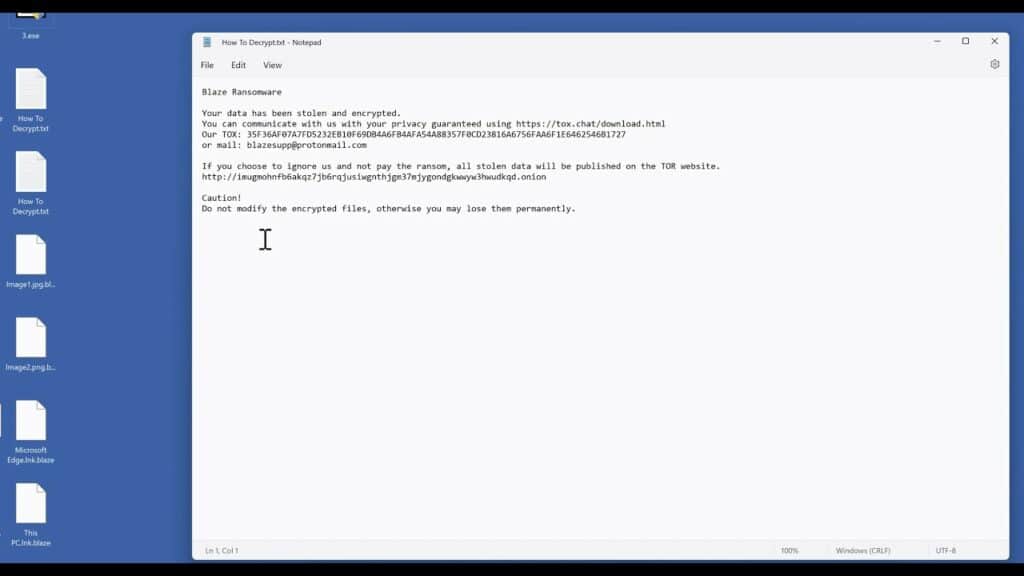
Blaze Ransomware
The Blaze ransomware is a relatively new group; it is a variation of the Babuk ransomware, a group that has made numerous attacks on businesses around the world. Blaze is following the path of its predecessor, the group targets large companies. The group uses phishing campaigns to break into the victim’s system, this tactic is targeted at specific companies, after
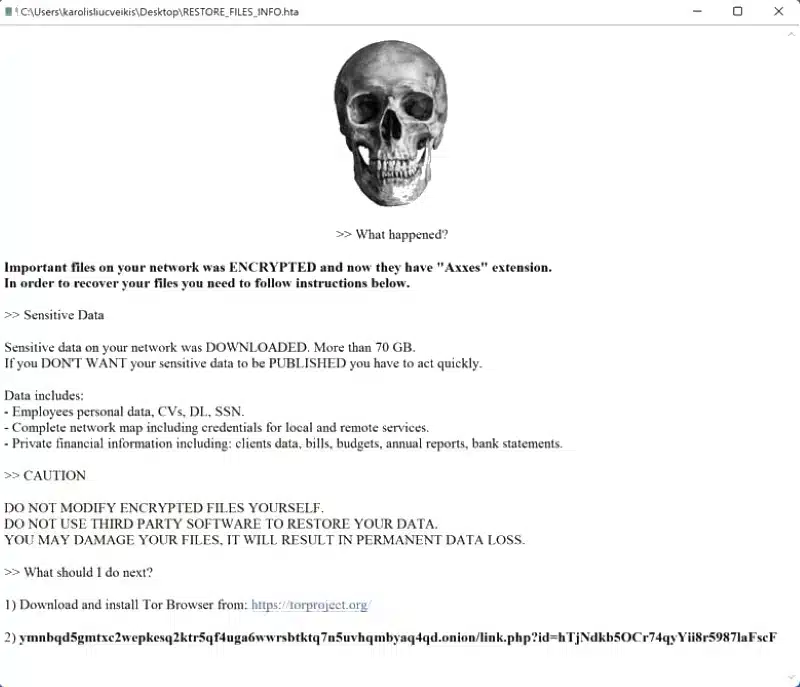
Axxes Ransomware
The Axxes ransomware has focused its attacks on businesses; the group uses the tactic of double extortion, which consists of stealing sensitive files and blocking them through encryption. After breaking into the victim’s system Axxes copies all stored files and sends them to a remote server controlled by the group, after which the original files are encrypted, thus completely blocking
