Expert Insights

Hellokitty ransomware
The HelloKitty ransomware, also known as FiveHands, has become quite relevant, to the point of drawing the attention of CISA and the FBI. The group was first spotted in December 2020 and remains active to this day. Their biggest publicised attack was on CD Projekt Red, an electronic game company known for “The Witcher” franchise. HelloKitty uses the Ransomware as
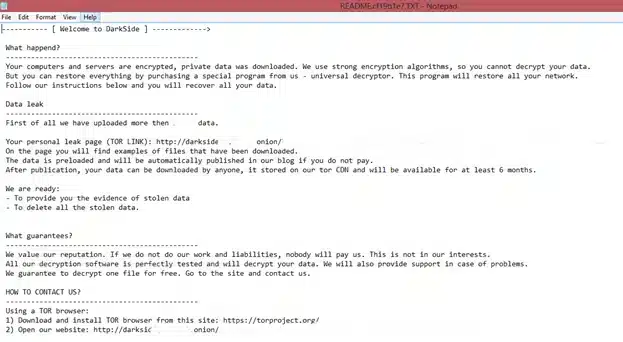
Darkside Ransomware
According to the data, the first appearance of the Darkside Ransomware happened around August 2020. Since then, the group behind the Darkside attacks has been targeting companies in all industries around the world. The vision of Ransomware as a Service (RaaS) is becoming more and more democratized among cybercriminals. It makes it possible for any malware owner to carry out
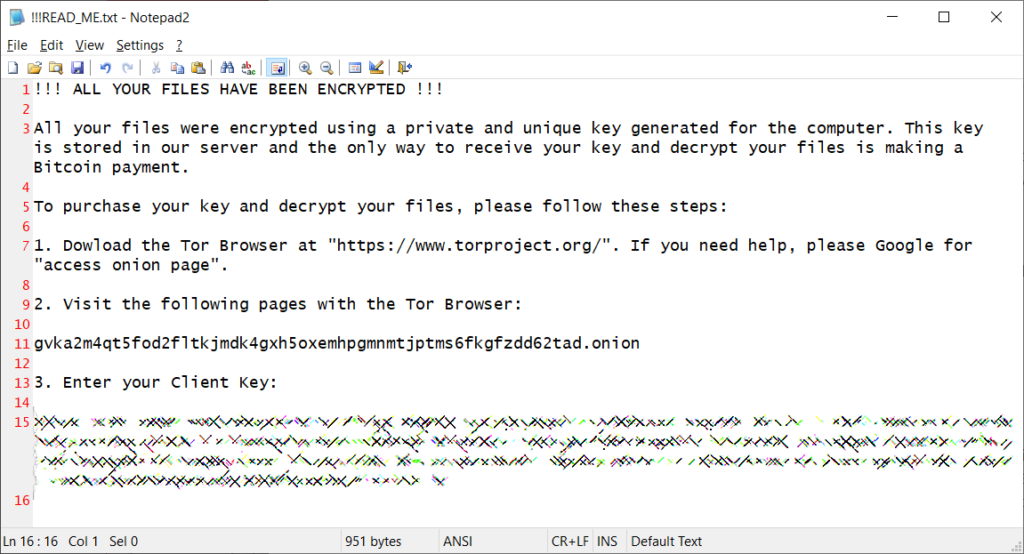
Qlocker Ransomware
The Qlocker ransomware has been active once again with waves of attacks this year. This ransomware has been using, like the others, the Ransomware as a Service (RaaS) strategy. This allows the destructive power of a ransomware attack to be made accessible to anyone. Qlocker’s primary target has been the specialized manufacturer of network storage solutions, QNAP. More precisely, the
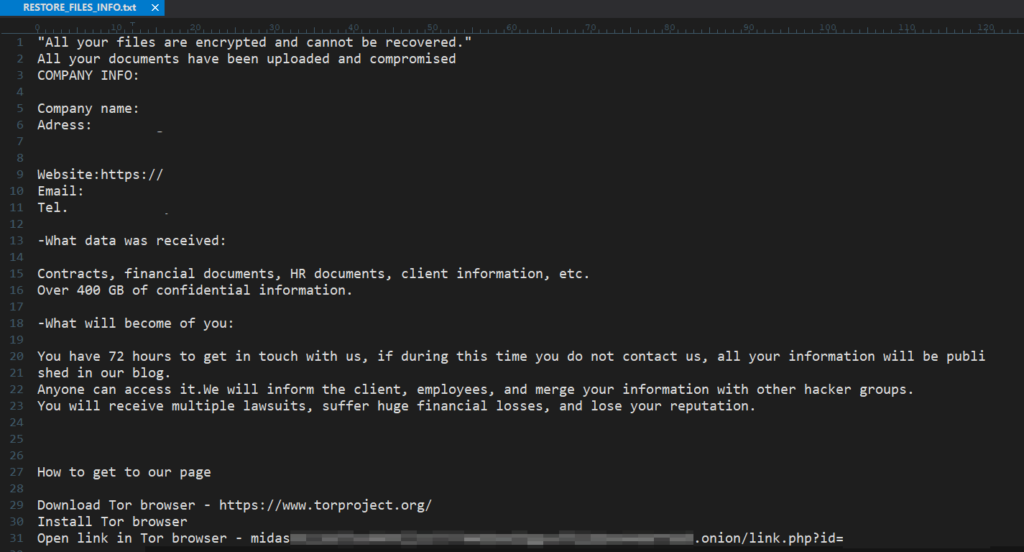
Midas Ransomware
The Midas ransomware is one of the variations of the Thanos ransomware that has emerged recently, Thanos was a large group that emerged in 2020, after numerous attacks the group disappeared, after a few months the source code of the malware was leaked, from this leak emerged the ransomware Prometheus, Spook, Haron and the newest of the group, Midas. There
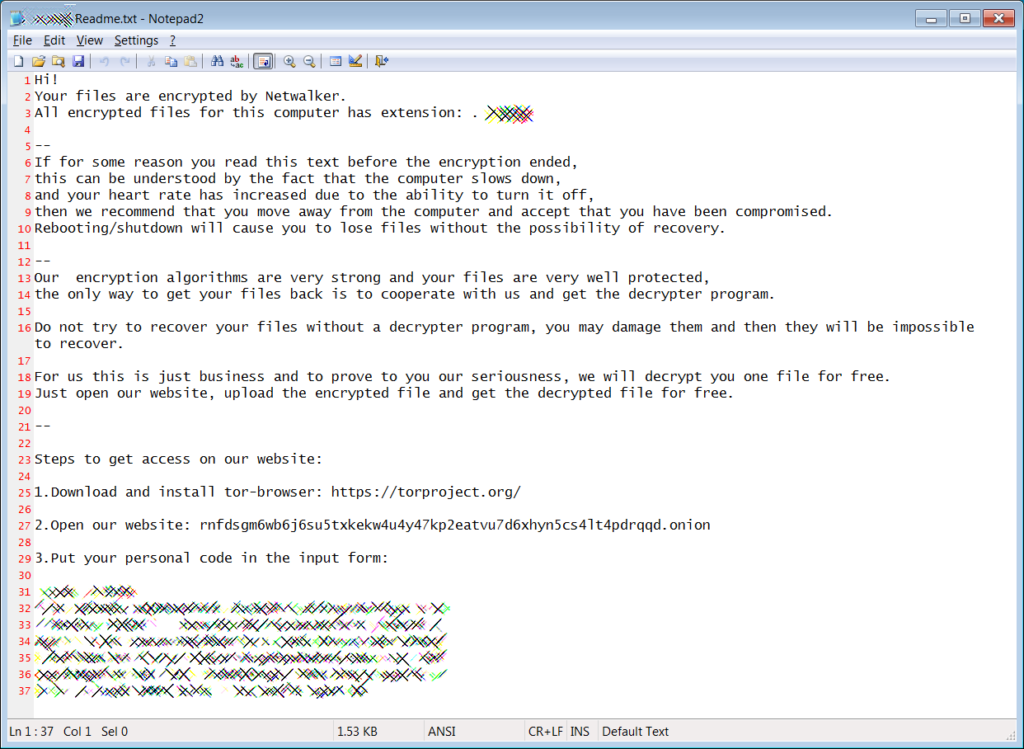
Netwalker Ransomware
Netwalker ransomware is among the big ransomware groups, together with REvil Sodinokibi, LockBit. 2.0 and Conti. The group has specialized in attacks on large corporations. The ransomware was created by the hacker group Circus Spider, which in turn is part of an even larger group, Mummy Spider. This structure shows that ransomware attacks have become a highly profitable business, attracting
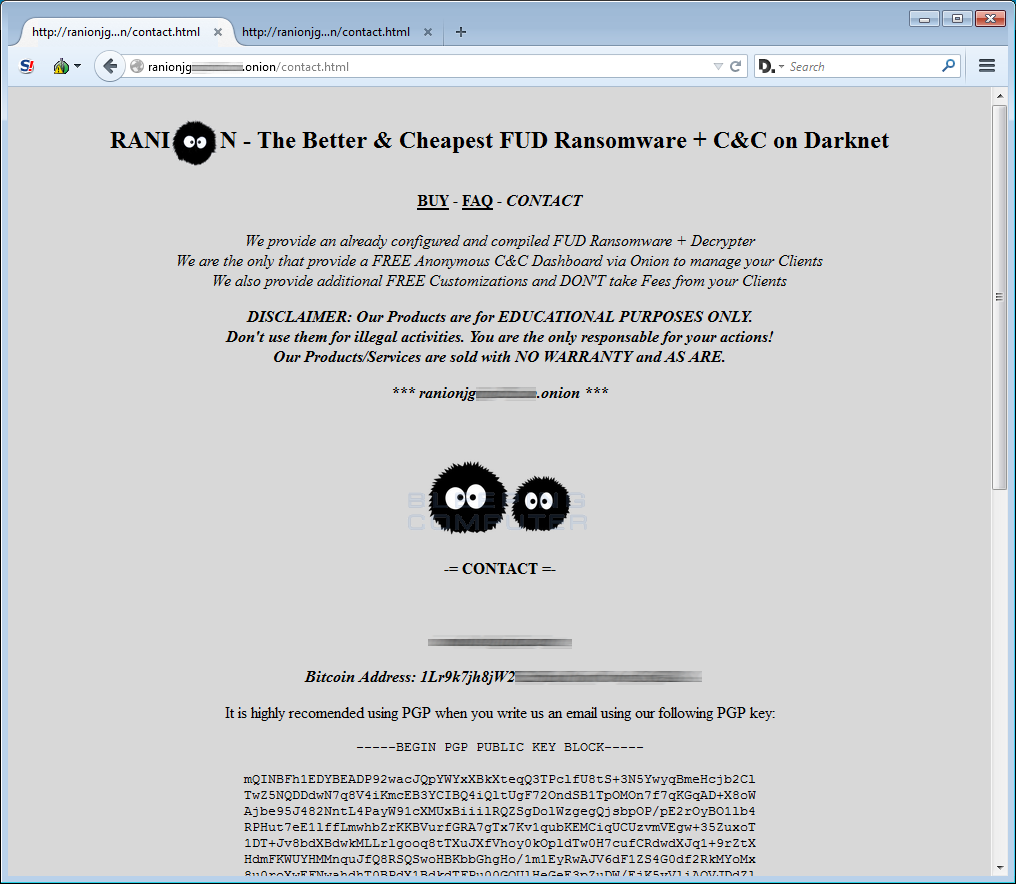
Ranion Ransomware
Ranion ransomware has drawn attention on dark web forums for its low sale price. The group works with the RaaS (Ransomware as a Service) tactic. The group has been offering free trial to its buyers, after which it is charged prices of 0.95 Bitcoin/year (US $960/year) or 0.6 Bitcoin/6 months (US $605/6 months). This easy access to a powerful ransomware
