Expert Insights

Xing Team Ransomware
The Xing Team Ransomware is a relatively new group, its first appearance was in 2021, it is a derivation of an old malware called Mount Locker. They have adopted the tactic of leaking the hijacked files, this data is posted on the group’s Dark web site. This type of tactic has been applied by the vast majority of ransomware groups,
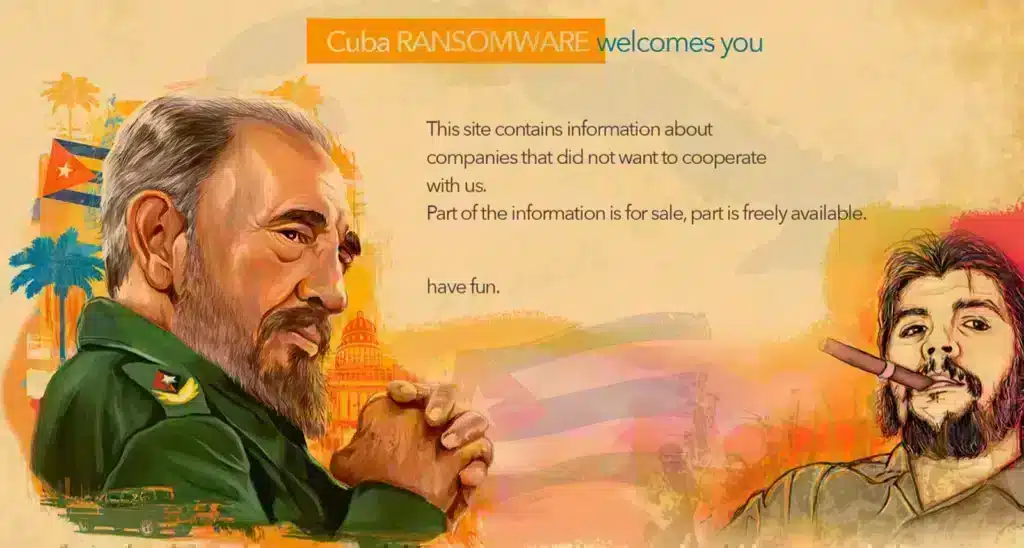
Cuba Ransomware
Cuba Ransomware targets the Windows operating system. It was discovered by Ravi, an American Ransomware hunter. Its attacks are carried out through email campaigns. The emails contain a link to “subscribe” to a service document, delivery of the malware is via this macro-loaded Word document, which contains a Hancitor payload, which is downloaded and opened. Hancitor is a downloader that
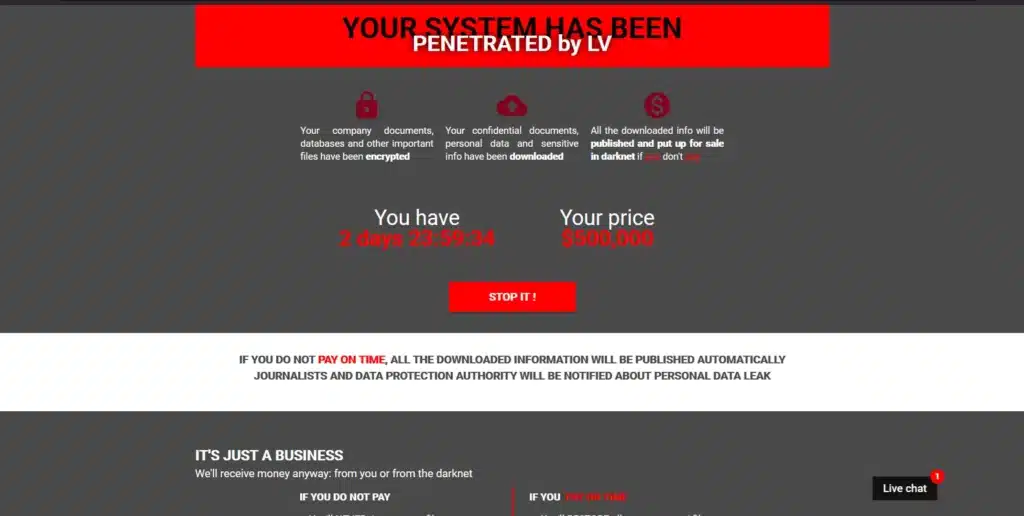
LV Ransomware
LV ransomware has its code structure based on the structure of the REvil Sodinokibi ransomware, which was the tormentor of numerous companies after a wave of attacks in the United States. After those attacks, the REvil group ceased its activities because of the attention its attacks received from the US government. It is unclear whether the group passed its code
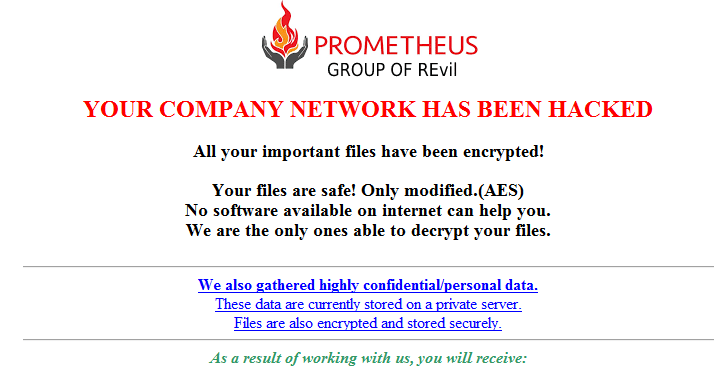
Prometheus Ransomware
The Prometheus ransomware first appeared in February 2021, the FBI has issued an alert about it. It is a variant of the Thanos ransomware and claims to be an extension of the REvil Sodinokibi group, but there is no concrete evidence of a link between the two groups. This tactic is used by newly created groups that do not yet
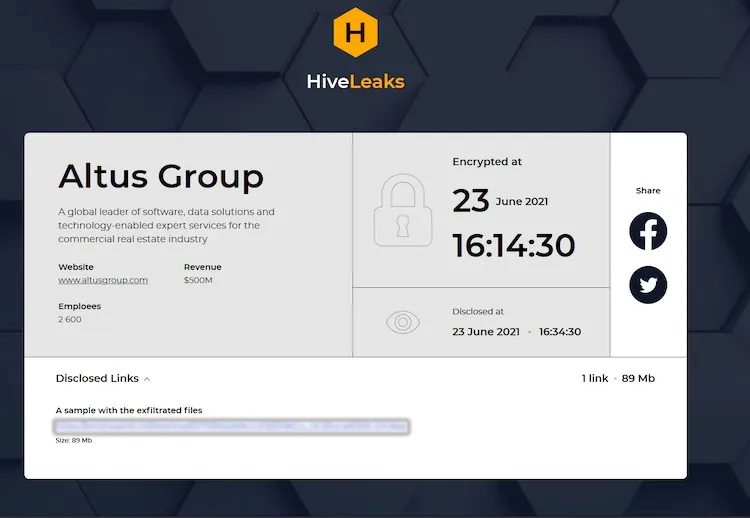
HiveLeaks Ransomware
A series of attacks by the HiveLeaks ransomware has garnered attention around the world, the FBI has issued a flash alert on attacks by this group. This extension is relatively new, their first appearance was in June 2021, they made a successful attack on Altus Group, a commercial real estate software development company, the amount requested for the ransom was

Vice Society Ransomware
The Vice Society ransomware attacks led to an update to the Windows print spooler code. The port the group used for their attacks became known as “PrintNightmare”, the Windows update aimed to close this port. This flaw was in the printing system, after failing to execute the Spooler the hackers could access the operating system which granted them the same
