Expert Insights

Ransomware MBC
The MBC Ransomware although little known is a group that practices large organized operations. There are several malicious malware spread across the internet, most of which infect random victims. However, MBC, like LockBit, does not carry out random attacks, but targets specific targets. In July 2021 MBC was able to hack and block Iran’s railway system, the hack brought transportation

Ransomware CoomingProject
The CoomingProject ransomware is a little-known group of malware that performs double extortion attacks. In addition to encrypting the victims’ data, the hackers steal and threaten to expose the information publicly if negotiation requirements are not met. It is worth noting that negotiating with the group is not recommended, as there is no guarantee of the release of the decryption

Ransomware KelvinSecurity
KelvinSecurity ransomware belongs to a very specific and not always malicious ransomware family. The term “Hacker” is probably familiar to you, but you may not have heard of the categories that these cyber experts fall into. We call them Black Hat, White Hat, and Grey Hat. This appellation is based on the old Western movies that were prominent in American

Ransomware SynAck
The SynAck ransomware is not particularly new. Its first appearances took place in the year 2017. At that time, the technology used in SynAck ransomware was very similar to other types of ransomware. The group behind the SynAck ransomware participated heavily in the evolution of ransomware attacks. In fact, you don’t have many reports of victims of SynAck ransomware
Ransomware Lilith
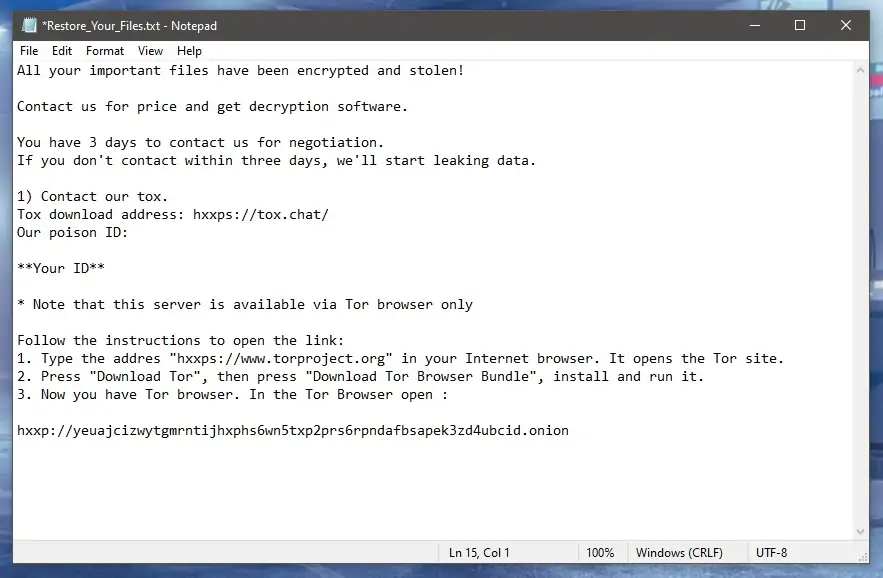
Lilith ransomware was discovered in June and has already been carrying out attacks on businesses using double extortion. When the ransomware is executed the encryption code begins infecting the files, adding the “.lilith” extension, and data is stolen and locked. Lilith targets machines that use 64-bit versions of Windows. A file with the ransom note is left by the group

Ransomware 0mega
0mega is a new ransomware extension released in May 2022. The group uses double extortion strategies, just like LockBit and other hacker families. The double extortion adopted by the ransomware variants, consists of not only charging a fee to recover the encrypted files, but the groups threaten to expose the victim’s data if the negotiation does not take place. The
