Expert Insights

Ransomware Daixin
A new ransomware called Daixin has been spotted in activity. There is not much information yet on its technical characteristics, but we already understand the impact Daixin ransomware can have on a company’s operation. Daixin’s first victim was a community hospital in Missouri, USA. Even before the hospital came forward, the Daixin group had already taken credit for the attack.

Ransomware NYX
Nyx ransomware is the newest variant recently discovered by cyber researchers. This new ransomware practices one of the most feared strategies for ransomware attack victims: double extortion. This refers to the fact that they not only encrypt the data, but also steal it. In this way they can exert greater pressure by threatening to disclose the stolen data if there

Ransomware Arvin Club
Ransomware that fits into the Ransomware as a Service (RaaS) system is extremely dangerous. The Arvin Club ransomware is part of this category. RaaS is the strategy for selling the malware, the creators sell their services on DarkWeb for a relatively affordable price. The big danger is that any malicious person, is able to operate a ransomware attack on any
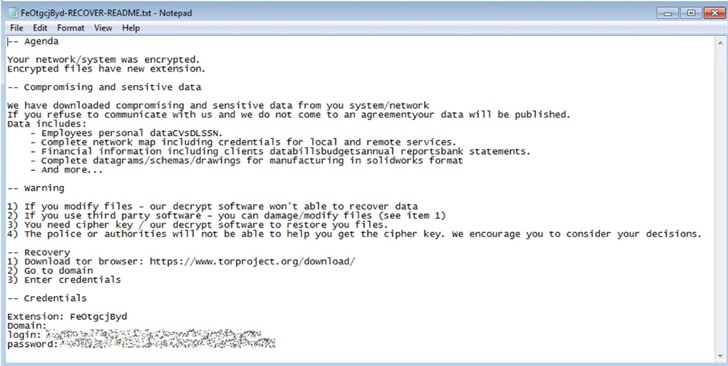
Ransomware Agenda
A new ransomware makes its appearance in the cyber world, the Agenda ransomware. Researchers have detected worrying moves on the part of this new group. In a short period of time they have already orchestrated several attacks targeting organizations in Asia and Africa. The Agenda ransomware was developed in the Go programming language. A language widely used by hackers to
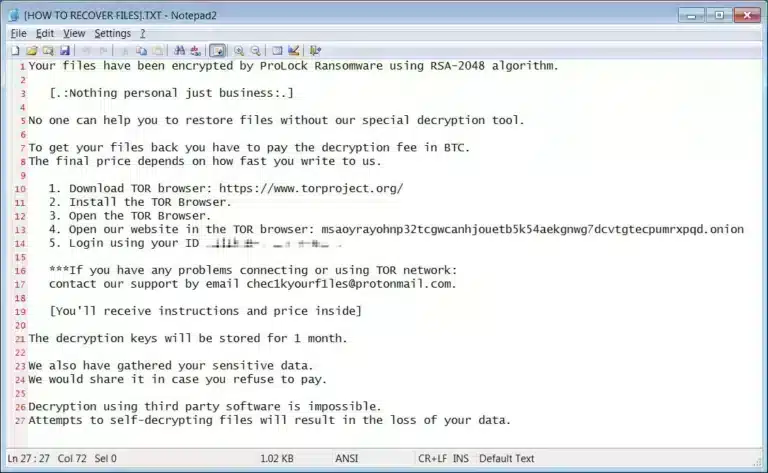
Ransomware ProLock
The ProLock ransomware follows a specific strategy when choosing its victims. This strategy is called “Big Game Hunting,” referring to the fact that the group only attacks large companies. This way, by having large companies or government networks as targets, the attackers are able to extract large payouts from the victims. By the end of 2019 ProLock was already active,
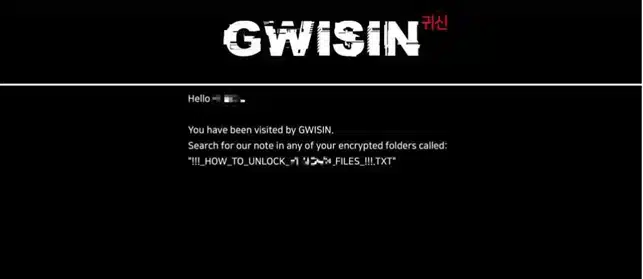
Ransomware Gwisin
Gwisin ransomware has been increasing the number of its attacks around the world. Asian countries, such as Korea, have been the target of an unprecedented wave of Gwisin ransomware attacks. Unlike other ransomware, Gwisin chooses and studies its victims very carefully. Each of them unknowingly undergoes a detailed analysis before being attacked. Gwisin ransomware is distributed in MSI installation file
